Both a credit lock and credit freeze can protect your credit report from being used for opening a new account or applying for a loan. If you’ve been victimized by identity theft, both are smart options. However, a credit lock vs. a credit freeze differ in their implementation. So, which one is right for you?
What Is a Credit Freeze?
A credit freeze is a free service guaranteed by law. When you initiate a credit freeze, most of your credit report will be limited. Lenders can’t evaluate your credit report until you lift or thaw the freeze. However, your credit report can still be viewed by companies responding to non-credit applications, your current creditors, debt collectors, and government entities. You can also still view your report if it’s frozen.
You can lift the credit freeze permanently or for a set amount of time if you are applying for a loan or a credit card. This can be as short as a day or a week, whatever you choose. However, with a credit freeze, you’ll have to lift it with each credit bureau individually. All bureaus handle lifting a freeze differently, so follow the appropriate steps for each one.
What Is a Credit Lock?
A credit lock is almost the same as a credit freeze but provides extra features and protections. Additionally, it can also come with a fee. You can initiate a credit lock with Experian, TransUnion, and Equifax:
- Experian CreditLock is available for $24.99 per month
- Equifax provides credit locks free to consumers through Lock & Alert
- TransUnion includes credit file locking for both your TransUnion and Equifax credit files for $29.95 per month
Some features of credit locks include notifications when anyone requests access to your locked credit report, alerts when your information appears on the dark web, identity theft insurance, and fraud resolution. Of course, each bureau offers different services but these additional features can offer you further protections.
How Do I Initiate a Credit Freeze vs. a Credit Lock?
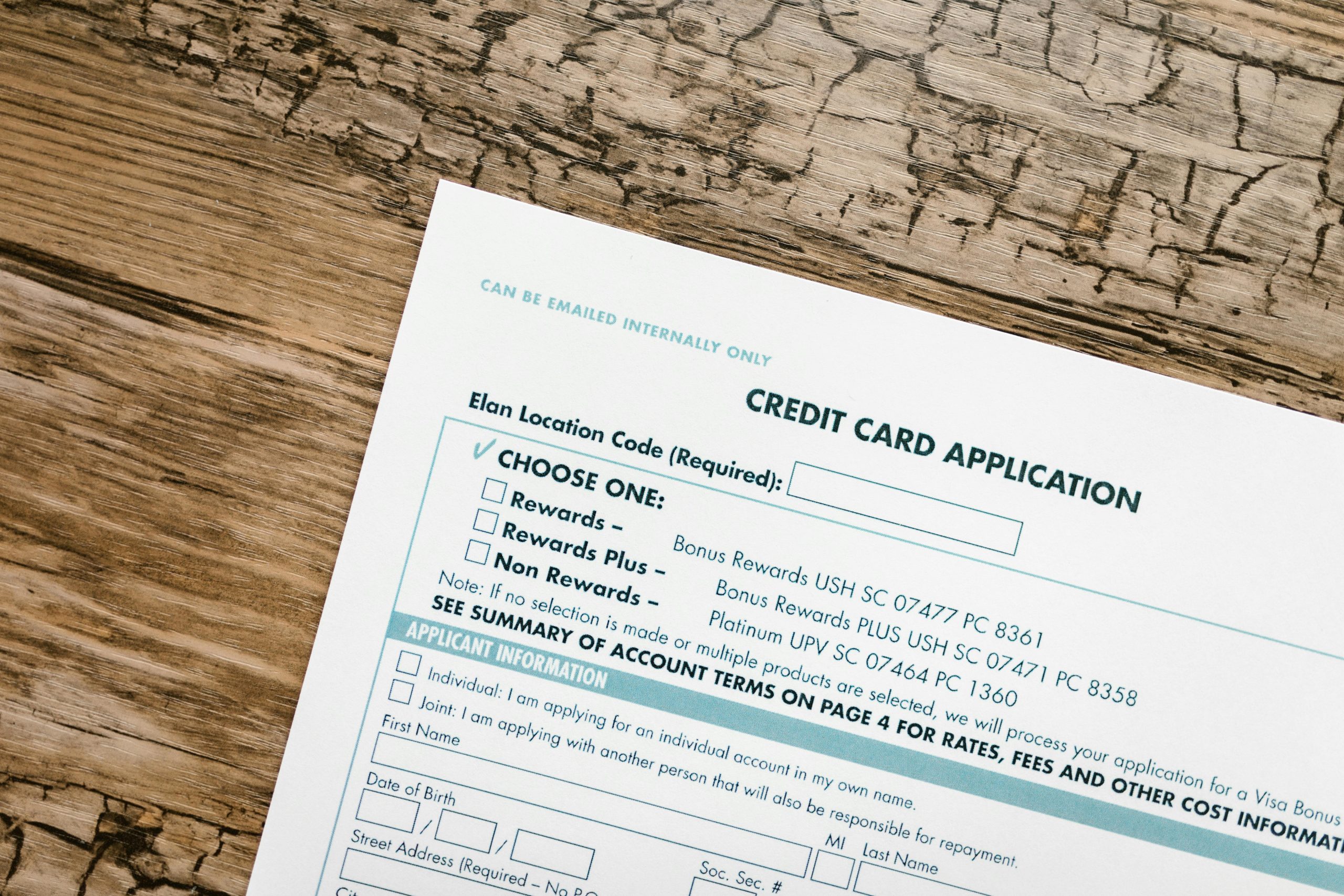
Initiating a credit freeze or a credit lock online can be as simple as a toggle on or off feature. You must sign up with each credit bureau to do so. You can also call each credit bureau or request a freeze or lock by mail. If so, you will need some accompanying identifying documents and information such as a recent utility bill, social security number, all your addresses in the last two years, your date of birth, and a government-issued ID.
When to Use a Credit Freeze vs. Credit Lock
If you suspect that you’ve been a victim of identity theft or your information has been compromised, both a credit freeze and credit lock are good options. However, a credit freeze is probably more appropriate if you don’t need additional features or don’t want to pay for a subscription. A credit freeze is also your only option if you are freezing the credit report of a minor. On the other hand, a credit lock can provide you additional protections and alerts. This can make dealing with the aftermath of identity theft more manageable.
Read More

Teri Monroe started her career in communications working for local government and nonprofits. Today, she is a freelance finance and lifestyle writer and small business owner. In her spare time, she loves golfing with her husband, taking her dog Milo on long walks, and playing pickleball with friends.